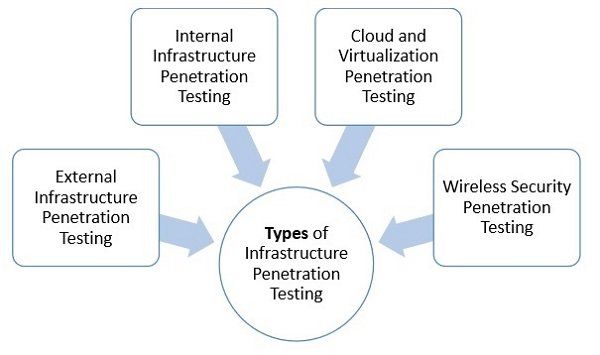
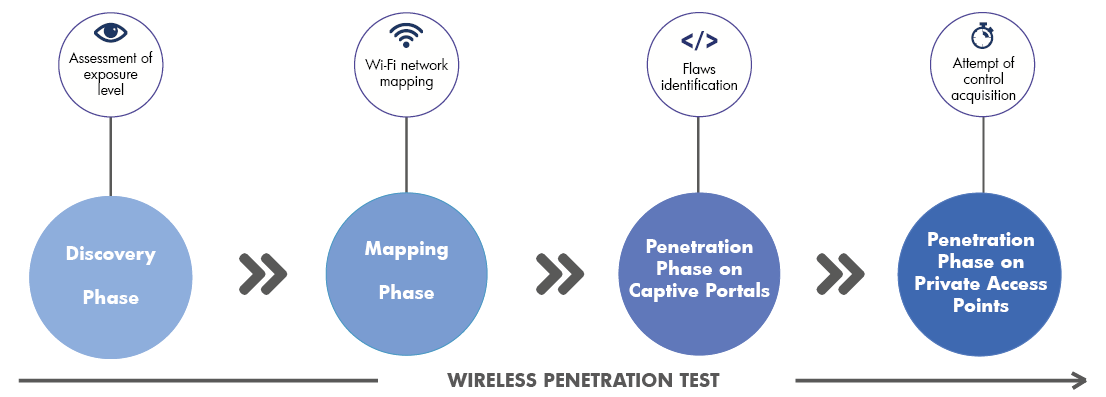
Wireless penetration testing





Wireless Security - Wi-Fi Pen Testing




Learn comprehensive wireless penetration testing, ethical hacking, and security through instructor-guided, technical, hands-on labs and up-to-date course.
5 Jan Penetration testing is like a car MoT or a service: it's a snapshot in time of the security posture of a given environment. However, whilst a.


Eliza Age: 34. Sexy ?? Sensual ?? SeductiveHey Guys!!I love sexy lingerie, high heels and the taste of good champagne in the company of quality gentlemen.Ullemoseparken- Rysllinge.


Jane Age: 18. h eSHE ENJOY SEX .I want to provide the best experience possible, so please take a look at my website to decide if I'm the right companion for you

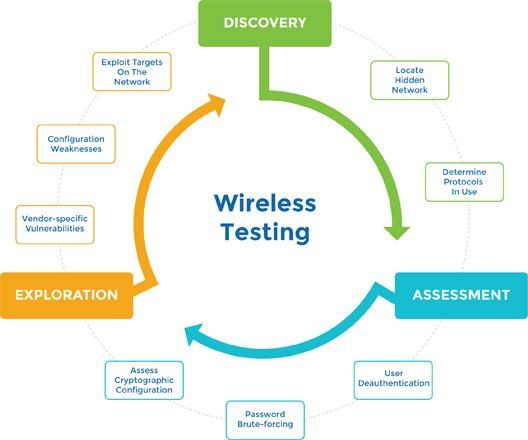
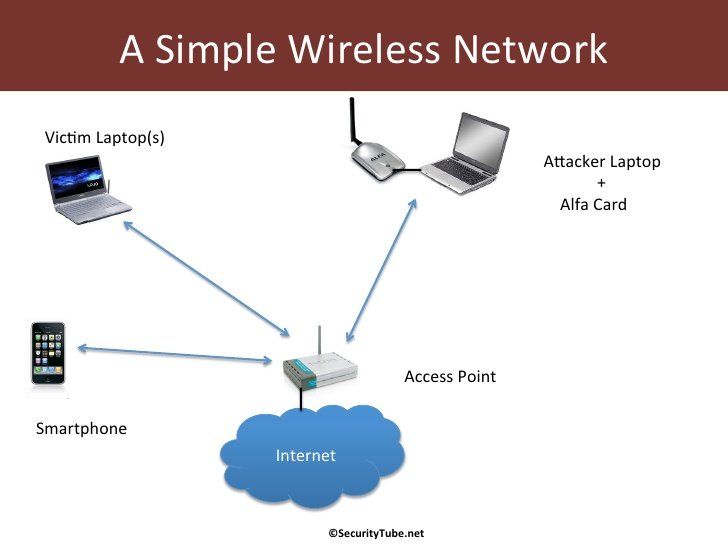
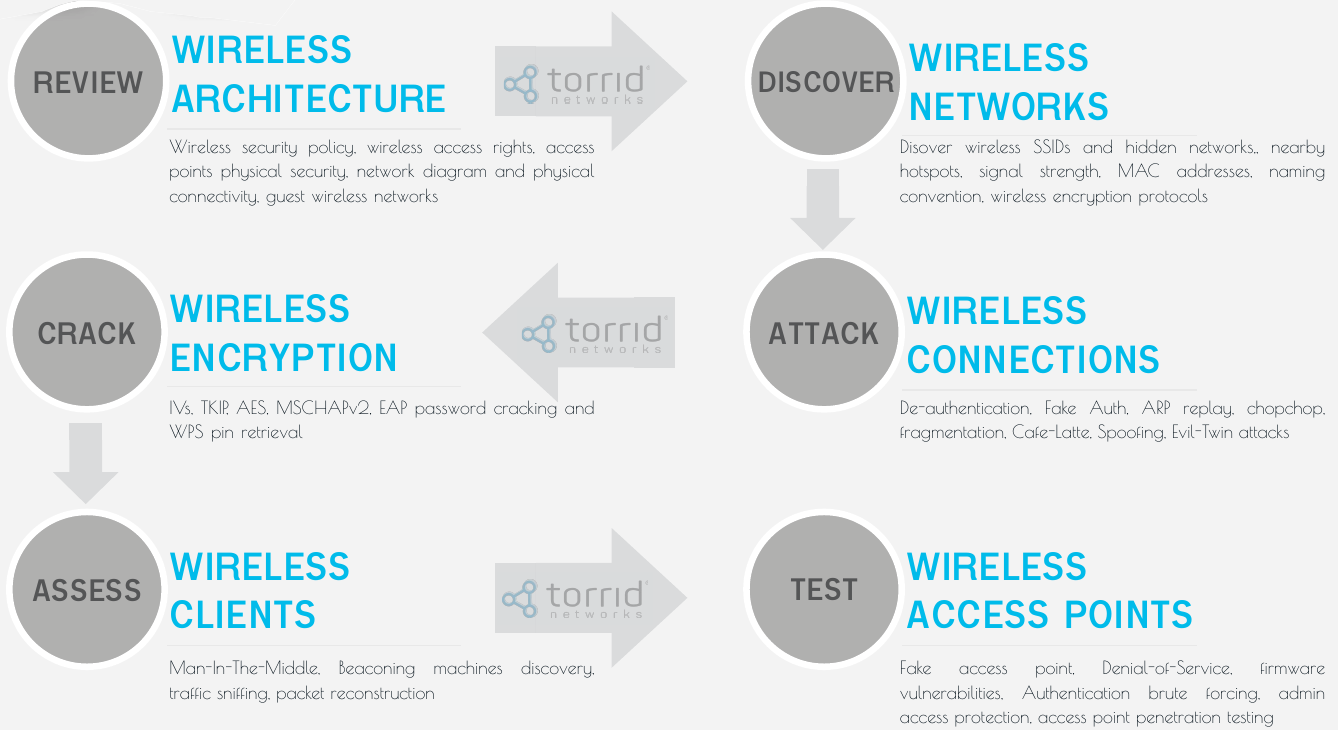
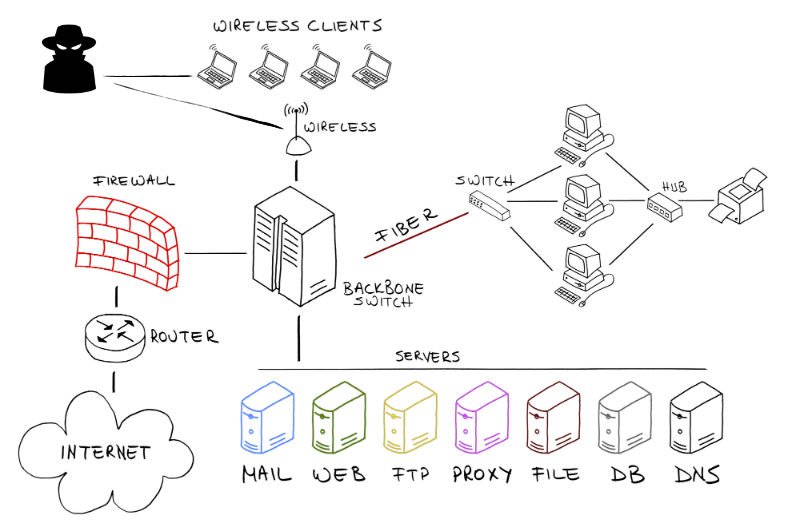
Description:Assess the configuration of legitimate access points. For me, the EliteBook and netbook both run Kali natively. What are we looking for? Monitor mode This is a critical aspect of wireless testing. To accomplish this, the IEEE designed a system of authentication and association for a client to permit easy hand-off of a client between multiple access points. Here is the list of the most commonly encountered wireless security faults and potential faults we look for:

























User Comments 3
Post a comment
Comment: