Penetration testing tool

Five Pentesting Tools and Techniques (That Every Sysadmin Should Know)
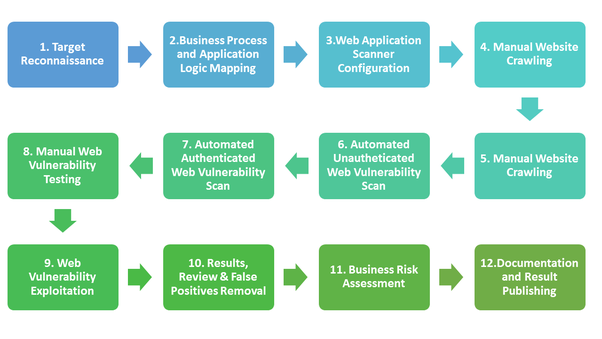
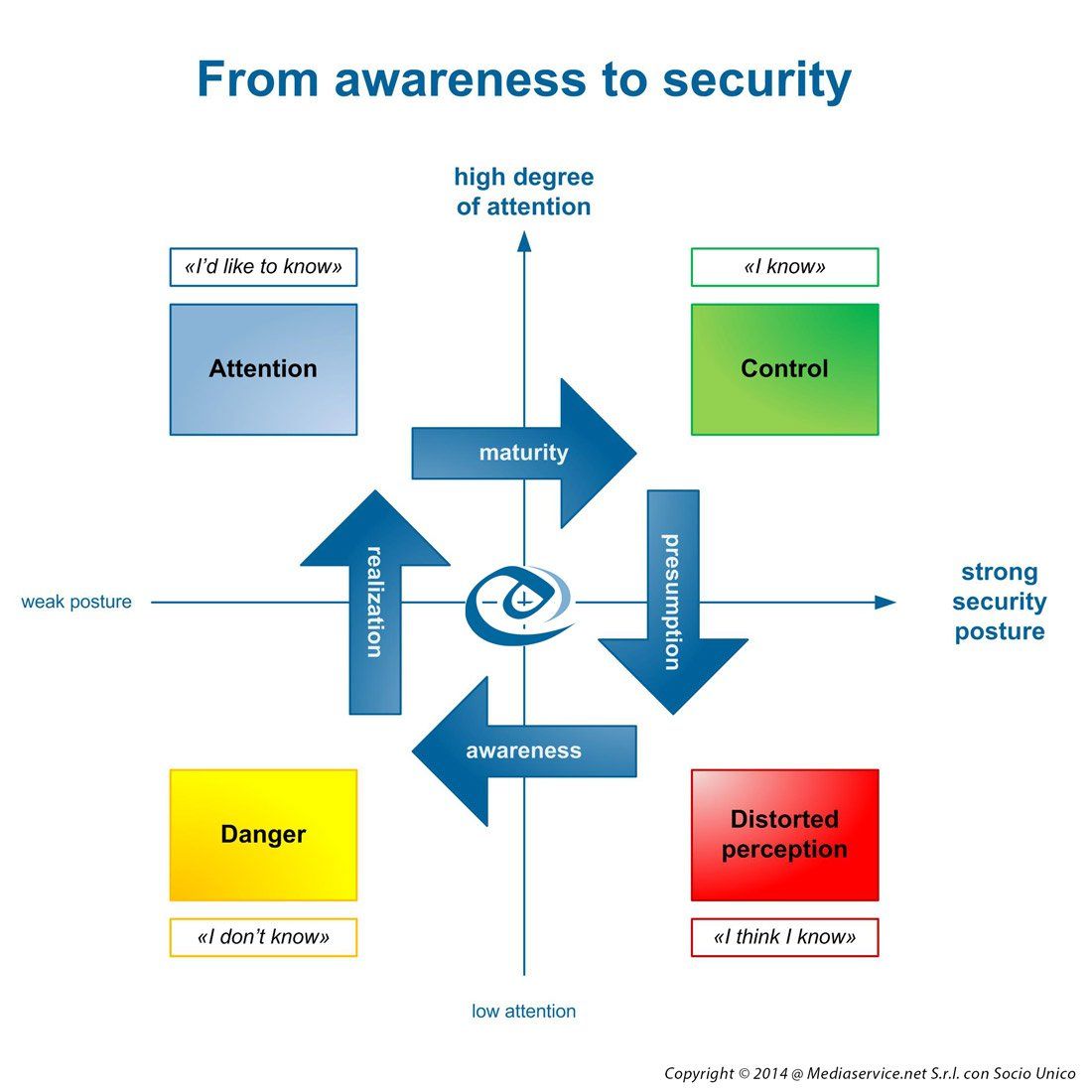
Discover security gaps through safely simulated attacks on your network





June Age: 21. I have the ability to make you feel at ease right away.Hi I'm hot and sexy ts here now in town avalable to night if you want make your dream come true and make your fantasy thing let meet and I can make it happens to you and give you good time enjoy with me to night see u guyWelcome to my world of independent singapore escorts
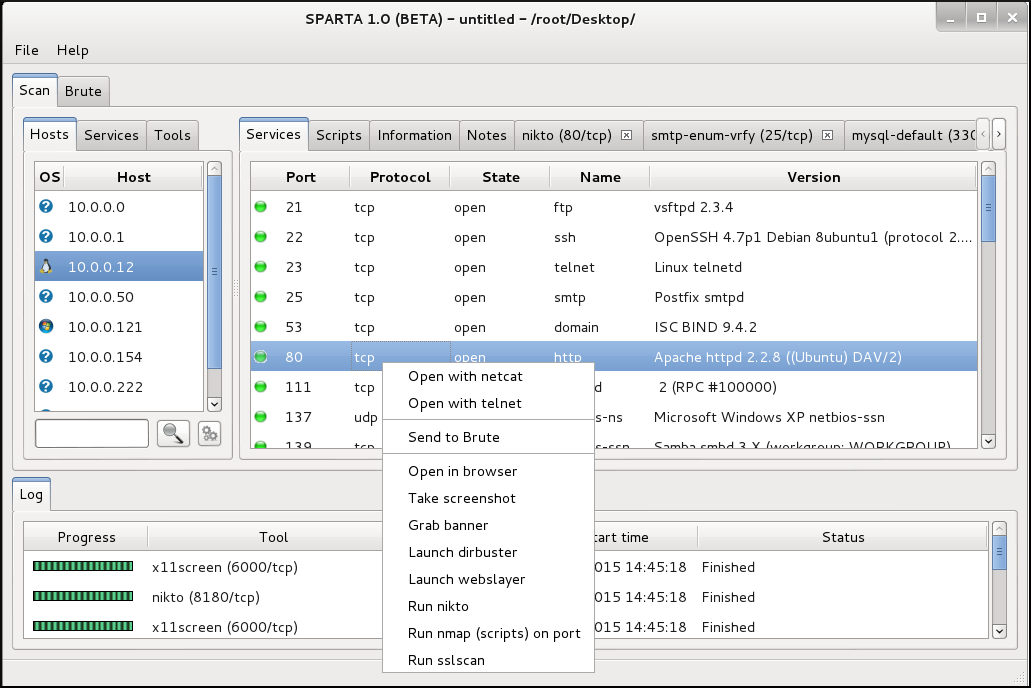
13 Sep We asked a few professional hackers for their thoughts on the best pen testing tools. Here's what they said.



15 Jun A list of all the best and most popular Pen Testing/Security Testing tools required for every penetration tester is addressed in this article.
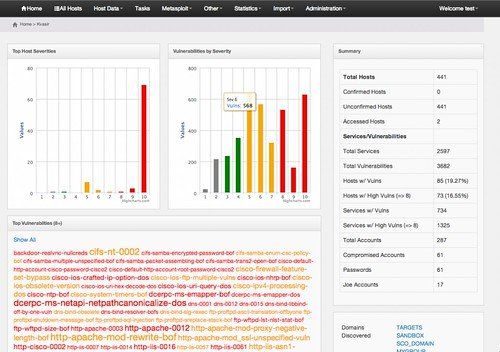
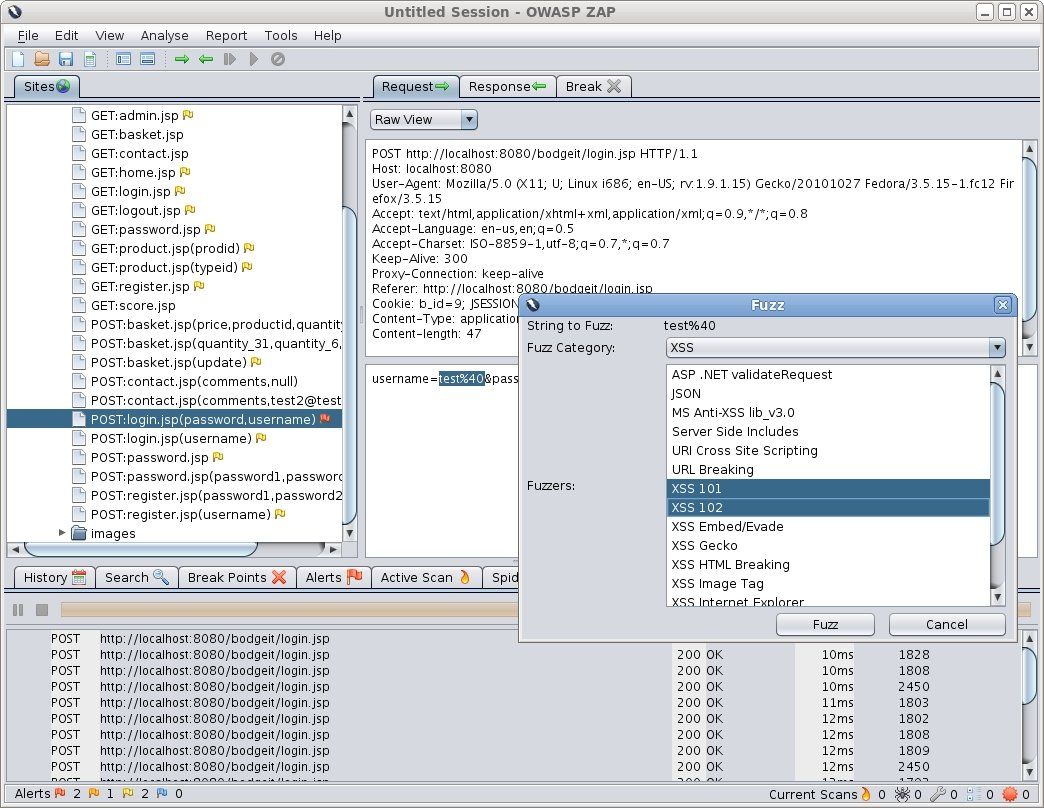
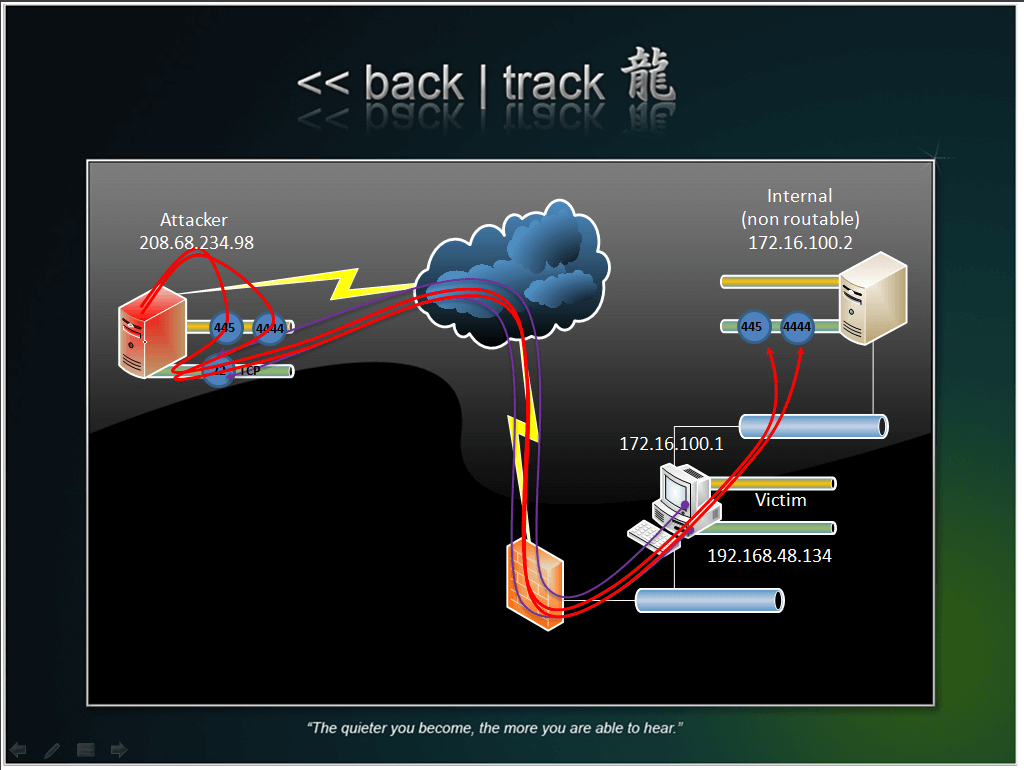
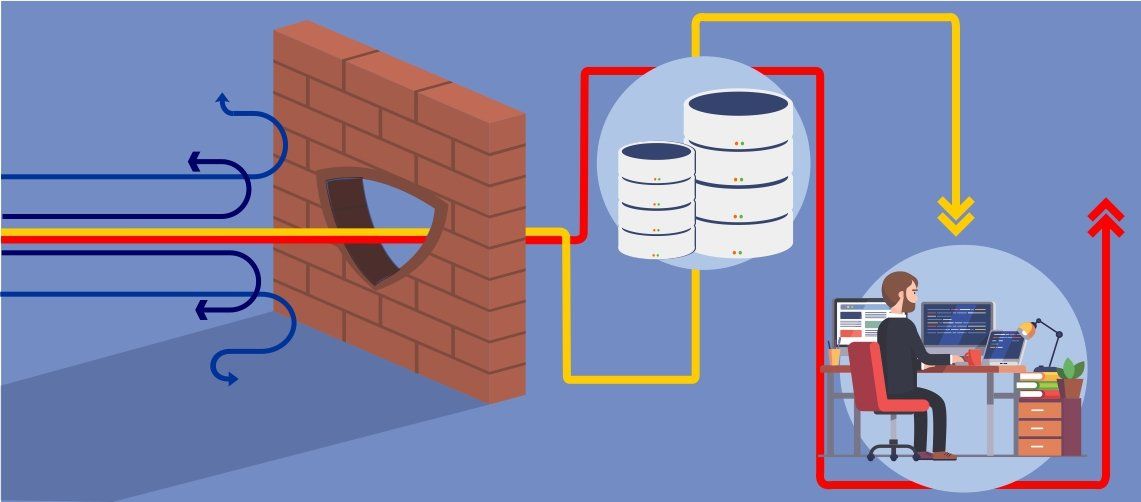
Description:Penetration Testing Toolkit Get a jump on the basics and best practices of penetration testing with nine free Rapid7 resources. Nessus Nessus is a popular paid-for tool for scanning vulnerabilities in a computing system or network. Can normal users launch PowerShell? Bypass network restrictions Even if you have all the tools on your machine, the local firewall of your network might block you from scanning external hosts. Penetration testing or pen testing refers to the technique of assessing the security of IT systems with the intention of discovering vulnerabilities—before attackers identify them.






















User Comments 4
Post a comment
Comment: